Overview
Integrated User Firewall provides a simpler way of getting an authentication source using a single-box solution via integration with Microsoft Active Directory.
As part of this feature, an administrator will be able to define policies and permit/deny based on the user logging into the network. This article explains how Junos Space Security Director is used to configure user firewall in security policies.
Prerequisites
Before user can start using Security Director, below settings must be configured on SRX(using CLI):
- Active Directory Access
- Access Profile
Refer this link for more info.
Feature
An administrator can specify a user as match criteria for the rule. SD provides the following predefined source-identities:
- any
- authenticated-user
- unauthenticated-user
- unknown-user
SD does not discover user information from Active Directory Server directly, but instead gets it from the SRX user authentication table. Currently, SRX does not load everything from Active Directory in the local cache, but gets the info of only those users or groups that are referred to in firewall rules. If a group is referred to then all its members will be loaded.
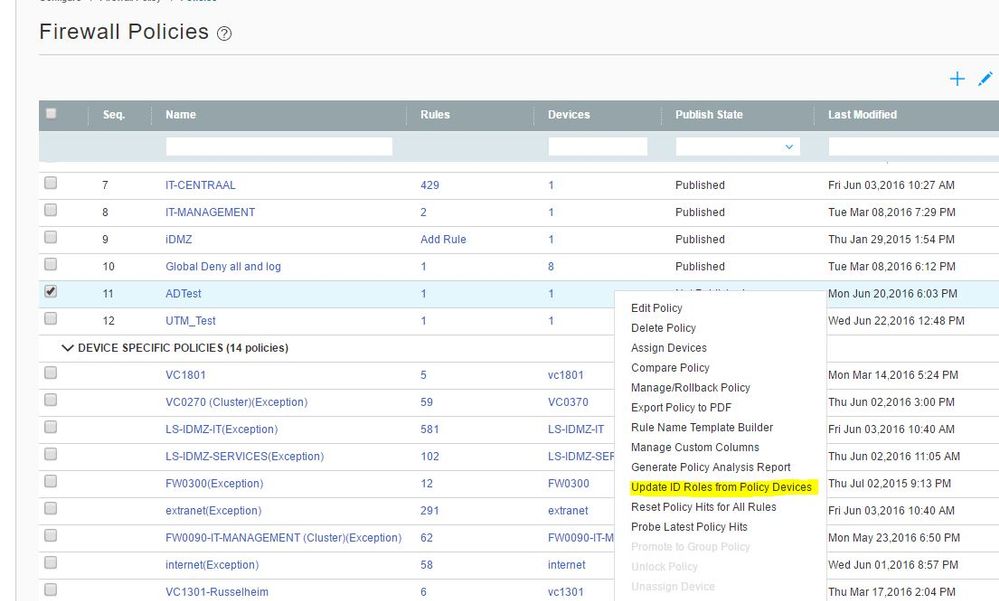
In SD a user can fetch a user's information from the SRX(s), as shown in following screenshot. All the SRX's assigned to the selected policy will be queried to provide cached user/groups info.
Note: Make sure matching schema is applied to SRX as the rpc calls are different depending on the junos version.
A user can provide a new value if it is not found in the existing list. Note that it will not create a user in the Active Directory. It is used only to refer to in the firewall rule.

Below is the sample CLI config generated by SD when user field(source-identity) is configured in security policies:
set security policies from-zone trust to-zone untrust policy p1 match source-address any
set security policies from-zone trust to-zone untrust policy p1 match destination-address any
set security policies from-zone trust to-zone untrust policy p1 match application any
set security policies from-zone trust to-zone untrust policy p1 match source-identity unauthenticated-user
set security policies from-zone trust to-zone untrust policy p1 then permit firewall-authentication user-firewall access-profile profile1
set security policies from-zone trust to-zone untrust policy p2 match source-address any
set security policies from-zone trust to-zone untrust policy p2 match destination-address any
set security policies from-zone trust to-zone untrust policy p2 match application any
set security policies from-zone trust to-zone untrust policy p2 match source-identity “nm.sdtest\rjnsandeep”
set security policies from-zone trust to-zone untrust policy p2 then permit
As mentioned earlier this feature provides visibility into who is accessing resources within an organization.
Security Director provides the following chart to monitor user activities, and the size of the bubble indicates the amount of bandwidth consumed by user. It also shows the top five applications for a given user. An administrator can quickly block a specific user or specific app(s) for any user using the same chart.
